Garmin has confirmed in an official statement that the recent service outage was caused by a cyber attack that has been affecting the company’s services since the 23rd of July 2020. The attack resulted in Garmin’s Connect services going down, while product call centres were also affected—which meant that online chats, calls, and emails have been unavailable over the past few days or so.
According to Garmin, no customer data was “accessed, lost, or stolen”, while functionality of their products have not been affected in any way—besides the ability to connect to Garmin’s online servers, of course. All of the affected systems are being restored as we speak, and “normal operation” is expected within a few days.
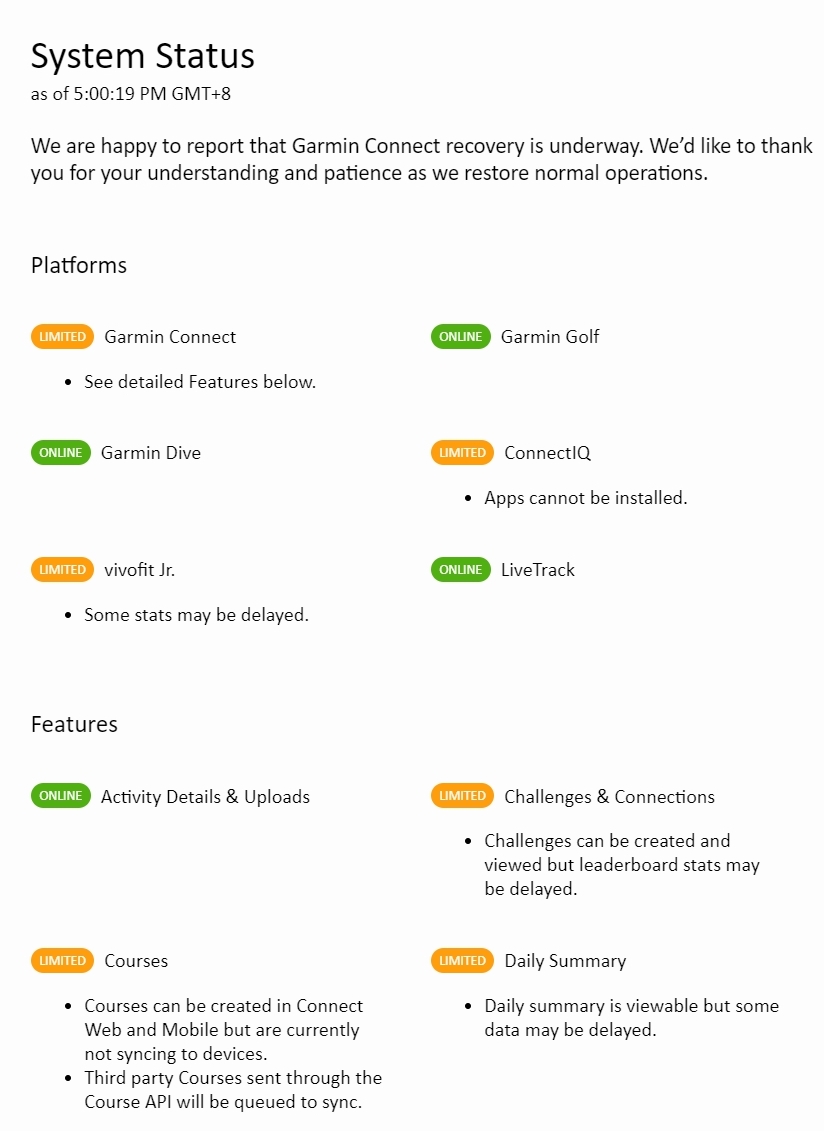
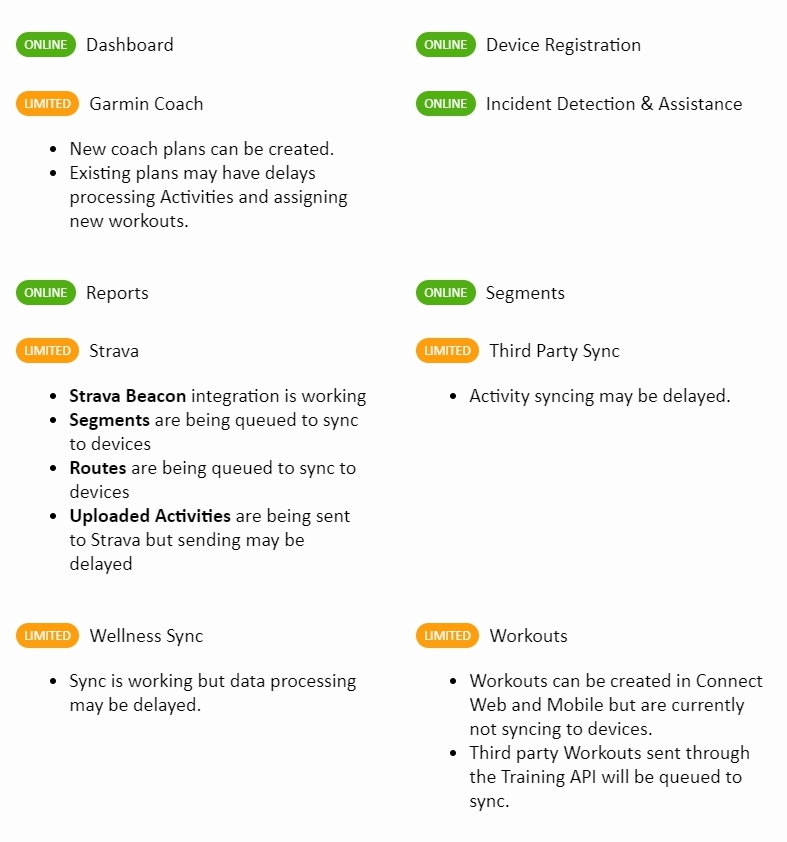
Referring to Garmin’s system status dashboard, roughly half of Garmin’s systems are already up and running, with a few features/platforms only performing at “limited” capacity. This means that for certain features, data may be delayed, or functionality may be limited. Here is the current status of Garmin’s services (accurate at the time of writing):
“Affected systems are being restored and we expect to return to normal operation over the next few days. We do not expect any material impact to our operations or financial results because of this outage. As our affected systems are restored, we expect some delays as the backlog of information is being processed. We are grateful for our customers’ patience and understanding during this incident and look forward to continuing to provide the exceptional customer service and support that has been our hallmark and tradition.”
Did Garmin pay a ransom?
While the company—whose products range from fitness trackers to navigation devices and more—hasn’t confirmed it, reports suggest that the attackers used ransomware called WastedLocker to attack Garmin’s servers. According to Bleeping Computer, a Russian-based group kown as Evil Corp has issued a ransom demand of USD10 million (~RM45.5 million) to the company.
Evil Corp is already a name on the radar of various authorities, with the group being sanctioned by the U.S. government in December 2019. As a result, Sky News reports that “U.S. persons” who transact with cybercriminals are subject to action from the authorities, although it isn’t clear if this would apply in cases of blackmail/extortion such as Garmin’s. As a result, Garmin have avoided discussing the issue, although it appears that the issue has been settled, with online services now resuming.
In fact, Garmin hasn’t actually used the words “ransomware” or “ransom” in any of its official statements, which seems to indicate that the company wants to keep its cards close for this particular issue. At the moment, there are two scenarios: Garmin paid the ransom (which would be in violation of U.S. regulations—Garmin is an American MNC), or they found a way to decrypt the malware without the attackers’ decryption key.
We’ve reached out to representatives of Garmin for comment, and will update this article accordingly.