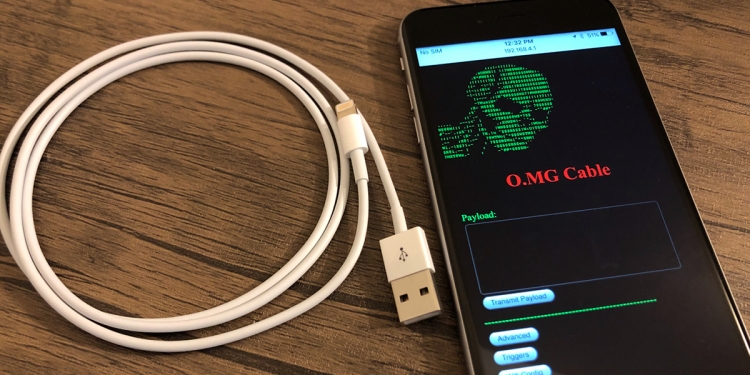
Okay, so this is pretty scary. At the annual DEF CON conference held in Las Vegas, Nevada, a researcher named Mike Grover showed off a Lightning cable that, for all intents and purposes, works as you’d expect it to. But these particular cables hide a little secret, and there’s a more sinister purpose for them other than charging up your iPhone or iPad.
MG, as the researcher is known as, revealed that the cable has actually been modified to include a security implant—one that lets him (or hackers) remotely access any computer connected to the cable. He further explained:
“It looks like a legitimate cable and works just like one. Not even your computer will notice a difference. Until I, as an attacker, wirelessly take control of the cable,”
Due to the fact it looks identical to a regular Lightning cable, the O.MG cable—as it is aptly named—can be swapped out or easily slipped into somebody’s set of cables pretty easily. And the early access prototype is actually on sale for just US$200 (about RM835), while there are plans to collaborate with online security store Hak5 to produce and sell more for US$100 (about RM417).
The way it works, the cables come with hidden hardware and software inside its USB connector, which can then be used by the hacker to remotely access the computer to then run any number of scripts and commands on the victim’s computer.
OMG! 2 months + 8 devs + O•MG Cable = malicious wireless implant update!
— MG (@_MG_) April 12, 2019
This update brought to you by the chaos workshop elves: @d3d0c3d, @pry0cc, @clevernyyyy, @JoelSernaMoreno, @evanbooth, @noncetonic, @cnlohr, @RoganDawes
More info: https://t.co/kkhUppsqiC#OMGCable pic.twitter.com/fIzOaKJSxL
“It’s like being able to sit at the keyboard and mouse of the victim but without actually being there,”
And of course, there have also been reports that the NSA has developed something similar themselves, although MG managed to do everything in the comfort of his own kitchen. The same modifications could theoretically be applied to any other cable as well, as MG states:
“Apple cables are simply the most difficult to do this to, so if I can successfully implant one of these, then I can usually do it to other cables.”
MG says that the cables are meant for security researchers, but as anyone could buy it, it does raise some concerns over who you should trust—if they were gifting you a brand new Lightning cable, that is. But by continuing to document his processes, perhaps security researchers can continue to develop protective measures even further.